Microsoft uses Secure Boot to safeguard your Windows PC from malware, attacks, and security vulnerabilities before your operating system fully loads. By default, Secure Boot is enabled on Windows PCs to verify that any software running in the Unified Extensible Firmware Interface (UEFI) is trusted and safe. The UEFI, in simple terms, is the basic firmware that launches to initialize your PC’s hardware and boot your operating system. The built-in Windows security protections aren’t active until the operating system fully boots, and that’s why Secure Boot is tasked with locking down the UEFI before that happens.
For more than a decade, Secure Boot did just that. The security tool was never bypassed publicly until late 2022 — beforehand, only researchers managed to identify ways to bypass Secure Boot. Everything changed with the BlackLotus exploit, which involved a UEFI bootkit with a Secure Boot bypass appearing for sale in October 2022. The exploit proved harder to patch than expected. Instead of “cracking” Secure Boot, bypass methods like BlackLotus use older and trusted bootloader versions with known vulnerabilities. Since these are official bootloaders trusted by Secure Boot, the security software doesn’t recognize them as a threat.
Security patches for vulnerabilities like this one aren’t shipped to Windows PCs by default. They require running PowerShell commands as an administrator, and come with grave operational risks. Both factors lead to both users and enterprises failing to manually apply the fix, leaving millions of Windows PCs with Secure Boot at risk of being bypassed.
Secure Boot is no longer unbreakable
Secure Boot has been bypassed on multiple occasions
It’s easy to think that Secure Boot is impossible to bypass, because for a decade, it was. Even now, bad actors don’t thwart Secure Boot by “breaking” it, per se. Instead, they find versions of the bootloader that are legitimate and signed, but contain critical security vulnerabilities. These downgrade attacks revert the Windows Boot Manager to an older version with the vulnerability an attacker wants to exploit. Since the Secure Boot system recognizes the older, but vulnerable, version of the Windows Boot Manager as official Microsoft software, it allows it to load.
From there, Secure Boot is bypassed, and attackers can run unsigned drivers or malware. This is how BlackLotus, the most famous Secure Boot bypass, managed to threaten millions of Windows 10 and Windows 11 PCs. It used a security vulnerability known as “Baton Drop,” tracked as CVE-2022-21894, to “take control of an endpoint from the earliest phase of software boot,” according to the U.S. National Security Agency.
Here’s how the NSA describes the Secure Boot bypass, which is still possible today, in a 2023 document:
Instead of breaking the Linux boot security chain, BlackLotus targets Windows boot by exploiting a flaw in older bootloaders — also called boot managers — to set off a chain of malicious actions that compromise endpoint security. Exploitation of Baton Drop (CVE-2022-21894) allows BlackLotus to strip the Secure Boot policy and prevent its enforcement. Unlike Boot Hole, the vulnerable bootloaders have not been added to the Secure Boot DBX revocation list. Because the vulnerable bootloaders are not listed within the DBX, attackers can substitute fully patched bootloaders with vulnerable versions to execute BlackLotus.
Aside from the technical jargon there, the important thing to know is that vulnerable bootloaders have not been added to the Secure Boot DBX revocation list. In other words, the older bootloaders with this critical security flaw are still trusted by Secure Boot today, even after updates. The Secure Boot DBX revocation list contains blocked code and certificates that were once signed, but are now known to be vulnerable.
It’s supposed to block untrusted UEFI modules from loading. However, since modules or certificates like the one used in the Baton Drop exploit are not on this list, they can still run — and Secure Boot can still be bypassed.
It’s an impossible choice for Microsoft
Revoking compromised Secure Boot keys can brick Windows PCs
By now, you’re probably wondering why Microsoft hasn’t added these flawed bootloaders to the Secure Boot DBX revocation list. Microsoft’s response to the Secure Boot bypass methods was quite slow, and an automatic patch for exploits like Baton Drop and BlackLotus still isn’t available. After BlackLotus hit the market in October 2022, an official security update didn’t reach Windows users until May 2023. That doesn’t tell the whole story — as Microsoft explains in a 2023 security update guide, the updated Windows Boot Manager isn’t enabled by default, and requires manual steps to activate.
Those steps aren’t exactly easy or user-friendly, even in 2026. Subsequent security updates, like one released for the Windows Boot Manager in July 2025, still do not enable fixes for CVE-2022-21894 automatically. As a Microsoft support document outlines, the process involves editing the Windows Registry, running PowerShell commands as an administrator, manually adding the affected certificates to the Secure Boot UEFI Forbidden List (DBX), and applying the Secure Version Number (SVN) to the firmware.
The average Windows user isn’t doing that — they probably don’t even know what the Windows Registry is or how to run PowerShell commands as an administrator. And that’s why Secure Boot can still be easily bypassed in 2026, years after the BlackLotus exploit became known. So, why isn’t Microsoft fortifying the Secure Boot with an automatic update?
What Microsoft isn’t telling the casual user is that securing the Secure Boot system with an automatic update could brick an unknown number of PCs and break compatibility with countless accessories. Some devices might not successfully apply the Windows Boot Manager or become inoperable. Additionally, recovery media or system backups stored as a CD/DVD, PXE Boot, or USB drive won’t work after installing the patch without a separate recovery media update.
If patching the exploit, which won’t affect most users, has the potential to brick computers and break compatibility with recovery media or backups, is it worth patching? Microsoft decided to leave that decision in the hands of Windows users, and that’s why it’s a manual process. Again, it’s also why Secure Boot is relatively easy to bypass, assuming the necessary conditions are met.

Your Windows PC might stop booting in June 2026 — here’s why and how to fix it
Ensure your PC boots safely before Secure Boot changes.
What you can do to protect your data
Update your BIOS regularly and set a BitLocker pre-boot PIN
These Secure Boot vulnerabilities require physical or administrative access to a Windows PC for exploitation, making real-world usage rare. On the flip side, someone with physical access to your PC could roll back the bootloader version to one vulnerable to Secure Boot flaws, and then run the exploit. Aside from manually applying the risky Windows Boot Manager update, there are a few steps everyone can take to secure their systems and protect their data.
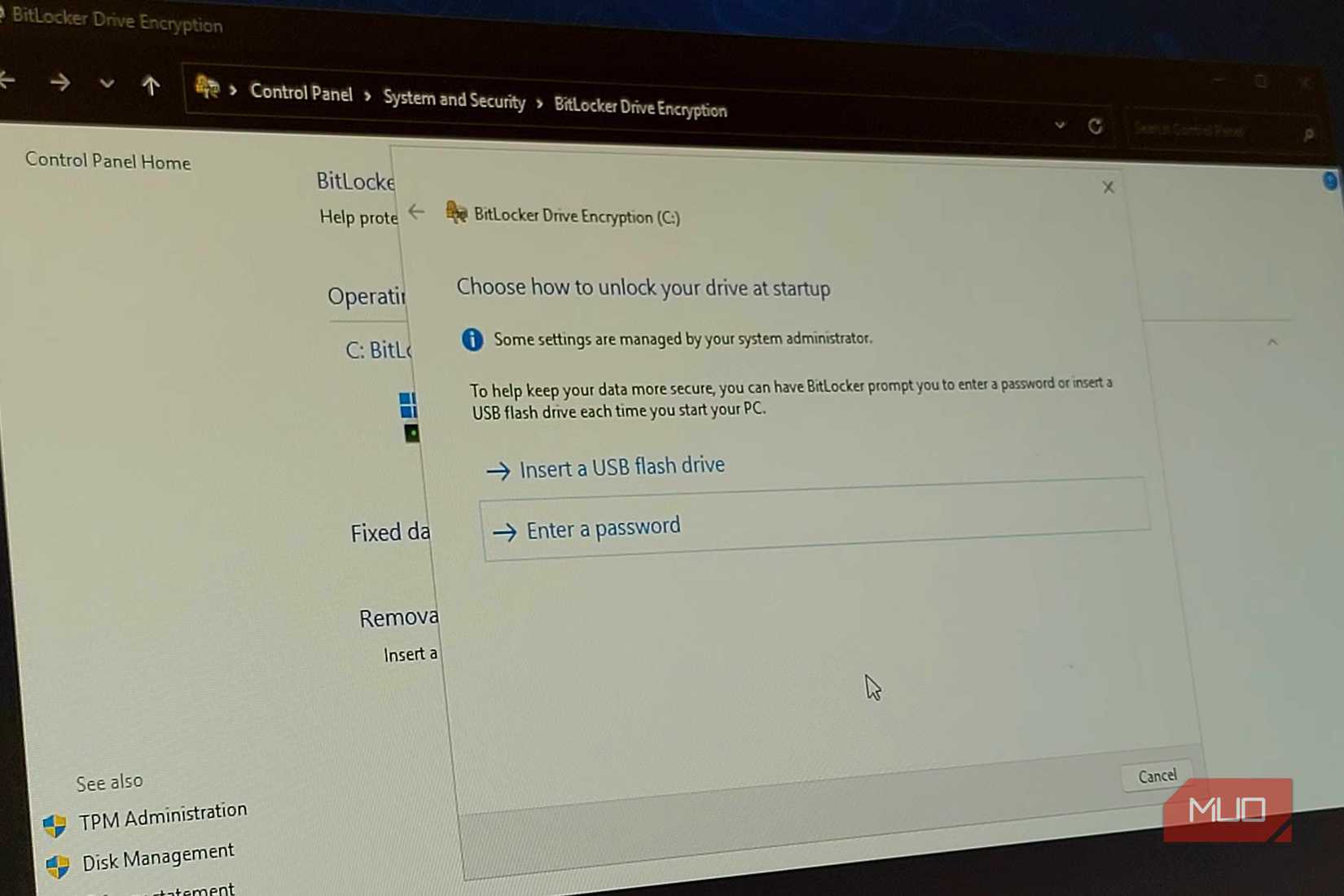
For one, keep your hardware in the right hands, and don’t plug anything into your PC that you don’t trust. The same premise applies within your operating system. You shouldn’t grant system administrator access to anything or anyone that doesn’t need it. To take preventative measures, enable BitLocker with a PIN to keep your data locked down even if Secure Boot is bypassed. Additionally, you could set your device up as a secured-core PC to secure the Windows kernel in the event the bootloader is compromised, but this requires the right components, like a TPM 2.0 chip and a supported CPU.
To sum up, Secure Boot is easy to bypass because attackers aren’t cracking it — they’re using official, trusted bootloader certificates with security vulnerabilities that can be exploited. Since revoking those certificates is a risky process, they are still trusted, and Secure Boot can still be bypassed.